TLP
TLP CLEAR
Author
David Deflache
Summary
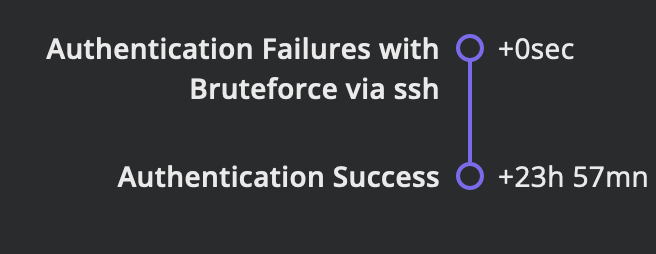
In this attack scenario, an individual with the IP address 192.168.0.42 and a valid username is engaging in an authentication brute force attack through SSH. Their target is a system with the IP address 192.168.0.111, using the default SSH port 22. The attacker executes a loop of 350 iterations, simulating numerous login attempts. Each attempt is marked as a failed login, triggering the action “User.LoginFailed.” A random delay between 3 to 5 minutes is introduced after each failed attempt. After the loop, there is a final pause of 3 minutes. The attacker then achieves a successful login, triggering the action “User.LoginSuccess.” This scenario illustrates an unauthorized access attempt through repeated SSH login trials. Can you detect it ?
DATA
TIMELINE
CATEGORY
Malware
references
- https://attack.mitre.org/techniques/T1110/
- https://www.cloudflare.com/learning/ddos/ddos-low-and-slow-attack/